Vibe Coding – Potential Risk Issues (2026)
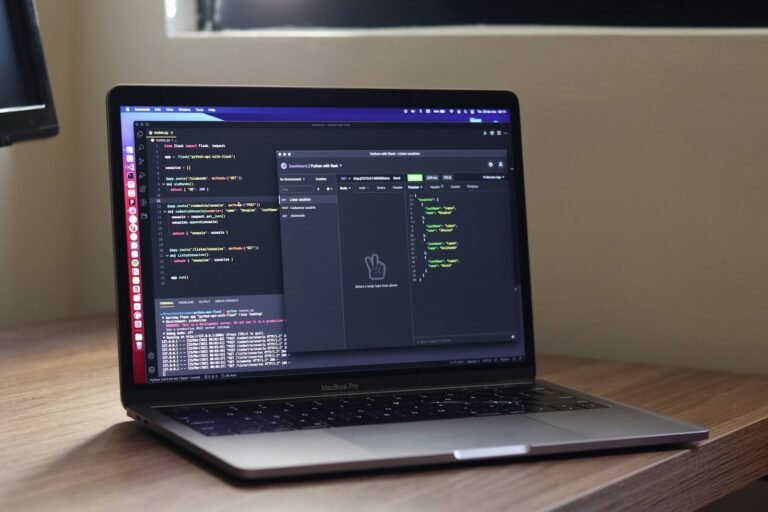
Vibe coding utilizes artificial intelligence to automate tasks on websites or in complex projects, making them more manageable. Developers and engineers use it extensively.
Vibe coding is growing rapidly among developers, engineers, and backend principal engineers. The use of AI is not inherently bad, but excessive AI can have a profoundly negative impact on businesses, particularly in certain areas. According to a recent survey, 40 percent of mobile web applications and API infrastructure built through wet coding are vulnerable, which has serious consequences, leading to many web applications being hacked. Cybersecurity and cybercrime experts predict that in 2026, applications built through wet coding will be hacked more frequently.
Among all these applications, the ones most at risk of being hacked include
- Python,
- Java,
- React.js JavaScript libraries (React)
- Node.js (JavaScript framework)
However, the JavaScript multiple frameworks, including ReactJS and Node.js, are facing multiple types of vulnerabilities regarding authorization bypass. However, after Vibe coding, these issues are increasing by more than 45%. Developers often miss multiple times when authorizing.
Many of these errors are API endpoints and API keys left inside JavaScript by front-end developers, which are later exploited by hackers.
Many of these errors are API endpoints and API keys left inside JavaScript by front-end developers. These API endpoints are later exploited by hackers, becoming a cause of data breaches and cyberattacks.
Common Security Risks in Vibe Coding
Authorization Bypass:
The biggest problem with API authentication bypass is that most code written with wipe coding is leading to authorization bypass vulnerabilities, where developers are leaving many API endpoints and local issues unaddressed, allowing hackers to easily exploit them.
5 Common example scenarios related to vulnerabilities commonly introduced during AI-assisted / Vibe coding, especially in React, Node.js,
1. Cross-Site Scripting (XSS) in React
AI-generated front-end code sometimes fails to sanitize user input in forms, comments, or search fields.
Example
// React componentreturn <div dangerouslySetInnerHTML={{__html: userComment}} />;
If userComment contains malicious HTML or JavaScript:
<script>alert('XSS');</script>2. Node.js NoSQL Injection
Example
// Vulnerable Node.js routeUser.find({ username: req.body.username, password: req.body.password }) .then(user => res.json(user));
If the attacker submits:
{ "username": { "$ne": null }, "password": { "$ne": null }}
3. Exposed Environment Variables via React Build
Example
// In .envREACT_APP_API_KEY=sk_live_12345// In codeconst apiKey = process.env.REACT_APP_API_KEY;
4. Insecure JWT Handling in Node.js
Example
jwt.verify(token, "secret", (err, decoded) => { if(!err) { next(); } else { res.status(401).send("Unauthorized"); }});
Impact: Privilege escalation, unauthorized access.
5. Broken Access Control in React + Node.js
Example
React frontend:
{user.role === "admin" && <button>Delete User</button>}
Node.js backend:
app.delete("/api/users/:id", async (req, res) => { await User.findByIdAndDelete(req.params.id); res.send("Deleted");});
If the backend does not verify the user role, any user can send a DELETE request directly to /api/users/123.
Impact: Full data deletion or modification without authorization.