If you’re planning to switch your career to penetration testing, which can be a fascinating career for you, before moving to a penetration testing role, you have to make sure which tool you are going to use for penetration testing in 2026.
HirePentester is a source of information platform where you can learn about multiple techniques that will work even in 2026 or 2027, whenever you are here. Whenever you move to API penetration testing, you have to remember one thing about APIs: what are the types of APIs? But when you get ready for the types of APIs, then you have to understand the architecture of different types of APIs and how they work.
Three Common Types of APIs
Here are three common types of APIs widely used across different sectors:
These three types—REST, SOAP, and GraphQL—are the most commonly encountered in API development and penetration testing.
And it’s also very important to understand that these three kinds of APIs are often used for different purposes and for different organizations: SOAP APIs, which are often used in the government sector.
These different kinds of APIs use different kinds of database systems to connect with each other. Now, in 2026, more than 100 million applications are using NoSQL databases. Before switching your career to penetration testing, you have to understand what databases are and the difference between different databases.
Some of the organizations that are using the Java framework Spring Boot are running Oracle at the medium level; organizations are using MySQL at the enterprise level, and sometimes they often use MongoDB.
APIs that are using NoSQL and SQL are easy to exploit, but sometimes it’s not necessary to have a NoSQL database there. Sometimes APIs with MySQL or SQL servers can be easily exploited by penetration testers.
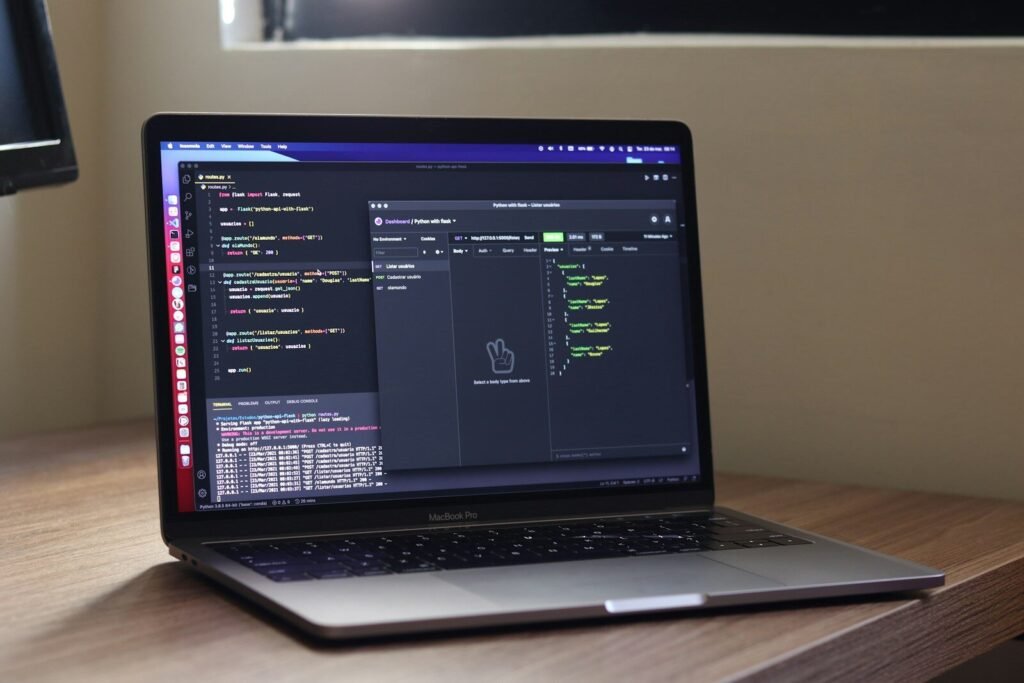
When it comes to selecting tools for API penetration testing, there are tons of tools available in the market. But it is not necessary to have some kind of classic tool for yourself. However, if your background comes with programming or you have a basic understanding of objects and classes, you can easily manipulate the data.
Choosing a tool for API penetration testing can be helpful for you; there are many open-source and closed-source tools available for testing.
However, all these tools come with powerful features, but they are not capable of handling every task on their own. Some work must still be done manually. For example, if you discover a parameter, you often need to test it manually. Tools like Burp Suite can assist in modifying and analyzing requests, but they cannot automatically find every vulnerability for you.
These tools are designed to make your work easier, not to replace your skills. If you expect them to identify everything on their own, that’s not going to happen.
| Tool | Type | Best For | Key Features | Supports Automation | Fuzzing | Auth Testing | Ease of Use | Limitations |
|---|---|---|---|---|---|---|---|---|
| Burp Suite | Proxy / Scanner | Full API & Web App Pentesting | Intercept requests, repeater, intruder, scanner | Yes (Pro) | Yes | Yes | Medium | Paid features required for full power |
| OWASP ZAP | Proxy / Scanner | Automated scanning & crawling | Spider, active scan, add-ons | Yes | Limited | Yes | Easy | False positives/negatives |
| Postman | API Client | Manual API testing | Collections, environment variables | Yes | No | Yes | Very Easy | Not designed for deep security testing |
| Insomnia | API Client | Debugging APIs | Clean UI, GraphQL support | Limited | No | Yes | Very Easy | Limited security testing features |
| Nikto | Scanner | Server misconfigurations | Detect outdated software and configs | Yes | No | No | Easy | No deep API logic testing |
| FuzzAPI | Fuzzer | API fuzz testing | Sends malformed payloads | Yes | Yes (Core) | Limited | Medium | Less known / limited ecosystem |
| SoapUI | API Tester | SOAP & REST testing | Functional + load testing | Yes | Limited | Yes | Medium | Heavy UI, slower performance |
| SQLMap | Exploitation Tool | SQL Injection | Automated DB exploitation | Yes | No | No | Medium | Only SQLi focused |
| JWT.io Debugger | Token Analyzer | JWT testing | Decode, verify, modify tokens | No | No | Yes (JWT only) | Very Easy | Limited to JWT |
| FeroxBuster | Enumerator | Endpoint discovery | Fast brute-force scanning | Yes | No | No | Medium | No vulnerability exploitation |